Author | Lucía Burbano
No city is immune to cyber-attacks, but these unfortunate events can be mitigated with a cyber resilience strategy. Here we shall have a look at the concepts of cyber resilience and three cities that have successfully implemented initiatives to combat cyber-risks.
What is cyber resilience?
Before delving into cyber resilience, we need to talk about cyber-risks, a very real threat in today’s global, digital and interconnected business environment. Areas such as the industrial sector, which works with technologies including the Internet of Things or have cloud data management strategies, are particularly vulnerable.
In order to protect businesses from hackers or from data filtrations, a cyber resilience strategy is required. The aim is to increase security, reduce the impact of a possible cyber-attack and continue to operate normally without suffering operational or economic losses.
Security covers much more than software designed to protect systems within companies. It involves people, processes and technology, which must be aligned in order to combat the threats.
The five pillars of cyber resilience
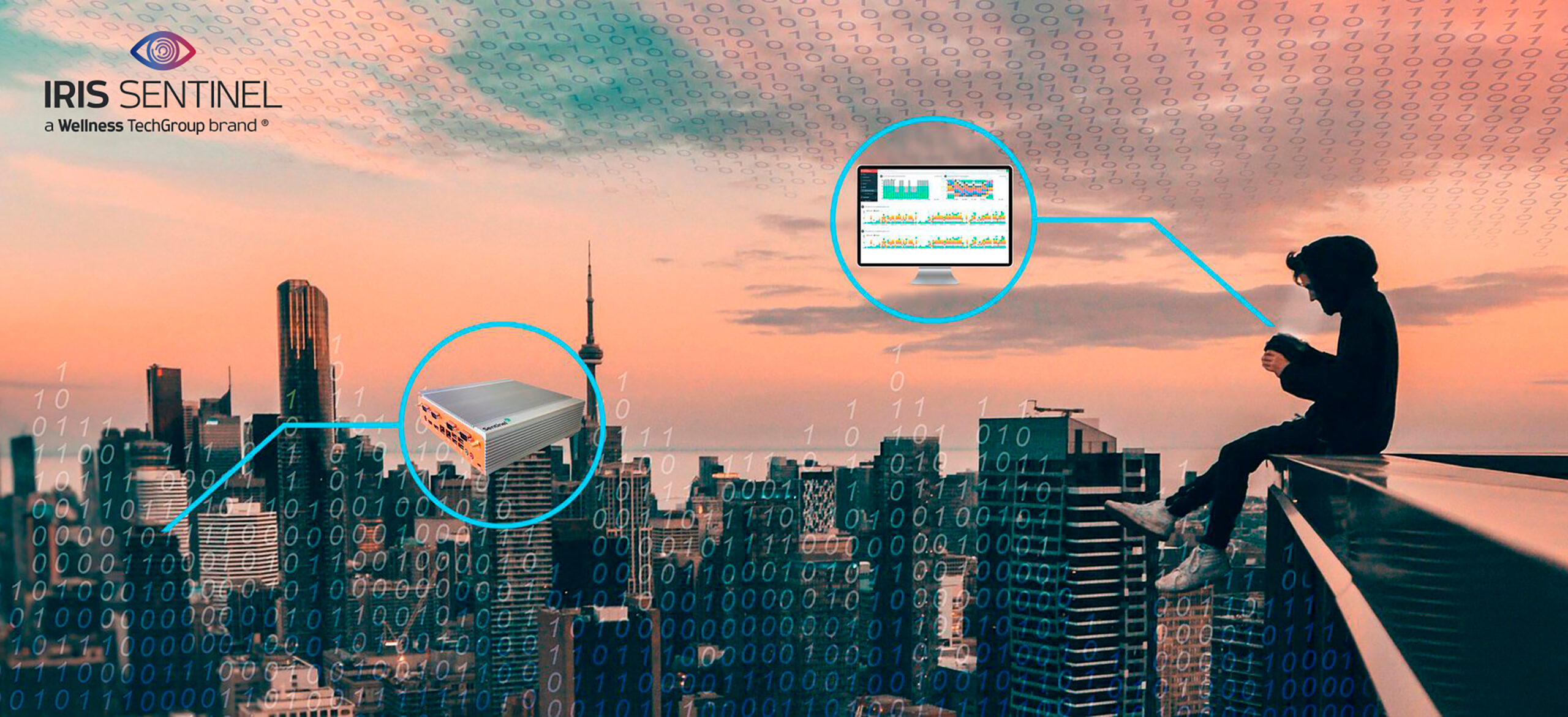
When we refer to cyber resilience strategies, there are five pillars that enable successful measures to be implemented:
1. Identify
Firstly, companies must have in depth knowledge of the level of security and potential risks. Therefore, the organization’s essential information has to be meticulously identified and the infrastructure and information has to be evaluated, including the level of sensitivity, vulnerability and risk tolerance.
2. Protect
It is time to implement the necessary protection measures. Protection measures for critical infrastructures and services have to be developed and implemented, with the aim of mitigating or reducing the level of vulnerability.
3. Detect
Appropriate actions must be implemented in order to rapidly identify an attack, evaluate the affected systems and guarantee a timely response. Furthermore, during this stage, the network must be continuously monitored in order to identify any other indicators related to that attack.
4. Respond
Organizations need a response plan, headed by a team of people with specifically identified functions and responsibilities.
5. Recover
This phase involves developing and implementing systems and plans to restore data and services that may have been affected during a cyber-attack.

Cities with successful cyber resilience strategies
Smart cities are particularly vulnerable, but many of these already have cyber resilience plans in place.. Below are some examples.
Atlanta
In March 2018, the U.S. city was the subject of a cyberattack that affected a significant number of devices connected to a specific network in the city. But Atlanta was prepared, since just a few weeks earlier it had held meetings with the FBI to evaluate the available cyber resilience programs.
When the attack occurred, they contacted numerous authorities that collaborated with the city. Atlanta had also just signed a cybersecurity insurance policy, which enabled it to access the necessary providers to execute the response and recovery pillars.
The Hague
The city in the Netherlands tackles this issue at various levels. Cybersecurity is firmly established in the city council itself at an operational, tactical and strategic level. Five of the main internal information security departments have a strategic advisory role in, for example, terms of procurement. This enables a common cyber resilience strategy to be applied for the entire municipality.
Manchester
The city in the northwest of England has been developing numerous initiatives designed to collaboratively combat cyberattacks. It has created a cyber foundry connecting four universities and the Greater Manchester Combined Authority to create an environment of digital trust in which to do business, increase the resilience of SMEs and use academic research as a technology accelerator.
It also participates in the Greater Manchester Cyber Advisory Group, a cross-industry group, and collaborates with Salford University’s ThinkLab. Lastly, the city council plays an active role in the promotion of cybersecurity measures among citizens and companies.